Governance refers to Data Governance in YOUnite.
What is Governance?
Governance describes the act of managing data access (i.e. who accesses certain data sets based on role, application, etc).
| Governance… | |
|---|---|
references |
where the federated data is stored |
provides |
visibility to data between zones and adaptors |
contains |
policies that get applied by the Data Governance Steward (DGS) as it moves through the YOUnite Data Fabric. |
ACLs and ACL Chains
ACLs are a key component of YOUnite and are different from permissions in that they control where data flows through the system. Permissions control who can manage zones, users, groups, permissions, and roles.
An ACL chain can be thought of as a series (chain) of policies (ACLs) that can be applied to a data event that occurs in the YOUnite Server.
ACLs
An access control list, or ACL, is a list of properties that when combined, create a policy that controls data flow between zones and:
-
Adaptors
-
Applications/services that have registered for data event notifications. The list of ACL properties includes:
-
Source Zone - The zone the data originated from
-
Source Adaptor - The adaptor the data originated from
-
-
Destination Zone - The zone the data is flowing to
-
Destination Adaptor - The adaptor the data is flowing to
-
-
Domain Version - The data domain the ACL applies to
-
Domain Version Properties - One or more properties in the data domain that are applied to the ACL
-
-
Data Records - One or more data records that are applied to the ACL
-
Allow/Deny settings for an ACL control which data events are either allowed or denied:
-
GET
-
PUT
-
POST
-
DELETE
-
Data event actions in YOUnite parallel the HTTP requests GET, PUT, POST and DELETE.
Not all ACL types use all of the ACL properties.
ACL Chains
ACLs are linked together to form ACL chains. They behave similar to network firewall chains but apply to an organizations data entities linked to YOUnite. When a data event occurs to a source entity, the change is transmitted to the YOUnite Router and the appropriate ACL chains are consulted and data is propagated (allowed) or restricted based on the ACLs in the ACL chains. Care must be taken to order the ACLs on a chain properly since the first ACL match is applied to a data event.
Types of ACLs
There are two types of ACLs:
-
Inbound ACLs
-
Outbound ACLs
Each zone has both an inbound and outbound ACL chain which are controlled by the zone data steward.
Outbound ACLs
Outbound ACLs can be thought of as policies on out-bound data. By default, all ACLs are open. Outbound ACLs are the controls a Source Zone’s data steward sets on Destination Zones:
| Data Event (Action) | Data Event Description |
|---|---|
PUT |
When the source zone allows or restricts the changes that occur inside the source zone from flowing outbound to destination zones. |
POST |
When the source zone allows or restricts new data that is created on adaptors in the source zone from flowing outbound to destination zones. |
DELETE |
When the source zone allows or restricts "deletes" that occur inside the source zone from flowing outbound to destination zones. |
GET |
What destination zones are allowed or restricted from using the source zone’s data when assembling data. |
Polices can be set on the following:
| Entity | Description | Default Value |
|---|---|---|
Source Zone |
The source zone is never set for an Outbound ACL since it is always the same as the zone that creates the Outbound ACL. |
n/a |
Source Adaptor |
The adaptor in the source zone where the data event originates. |
ALLOW ALL |
Destination Zone |
The destination zone where the data event can be delivered (i.e. it has adaptors that are capable of handling the event) |
ALLOW ALL |
Destination Adaptor |
An adaptor in the destination zone capable of handling the data event. |
ALLOW ALL |
Data Record (DR) |
One or more federated data records that belong to the Domain Version. |
ALLOW ALL |
Domain Version |
The domain version the ACL can be restricted to. |
ALLOW ALL |
Domain Version Property |
One or more properties in the data domain that are applied to the ACL |
ALLOW ALL |
Allow GET / Restrict GET |
Allow or restrict GET data events. |
neither is set |
Allow PUT / Restrict PUT |
Allow or restrict PUT data events. |
neither is set |
Allow POST / Restrict POST |
Allow or restrict POST data events. |
neither is set |
Allow DELETE / Restrict DELETE |
Allow or restrict DELETE data events. |
neither is set |
|
Note
|
To specify ALL use the constant string "00000000-0000-0000-0000-000000000000".
|
Inbound ACLs
Inbound ACLs can be thought of as policies on in-bound data. By default, all ACLs are open. Inbound ACLs are the controls a Destination Zone sets on Incoming data requests from Source Zones:
| Operation | Data Event Description |
|---|---|
PUT |
When the destination zone allows or restricts changes that occur in source zones/adaptors from flowing into the destination zone. |
POST |
When the destination zone allows or restricts new data that is created in source zones from flowing into the destination zone. |
DELETE |
When the destination zone allows or restricts deletes that occur in source zone/adaptors from flowing into the destination zone. |
GET |
What source zone/adaptors are allowed or restricted (ignored) by the destination zone when assembling data. |
Policies can be set on the following - the zone data steward in the destination zone, creates the ACL on behalf of the destination zone:
| Entity | Description | Default Value |
|---|---|---|
Source Zone |
The originating source zone. |
ALLOW ALL |
Source Adaptor |
The originating source zone’s adaptor(s). |
ALLOW ALL |
Destination Adaptor |
An adaptor in the zone the ACL belongs to that is capable of handling the data event for the given domain version. |
ALLOW ALL |
Domain Version |
The domaOne or more properties in the data domain that are applied to the ACL |
ALLOW ALL |
DR |
One or more federated data records that belong to the Domain Version. |
ALLOW ALL |
Allow GET / Restrict GET |
Allow or restrict GET data events. |
neither is set |
Allow PUT / Restrict PUT |
Allow or restrict PUT data events. |
neither is set |
Allow POST / Restrict POST |
Allow or restrict POST data events. |
neither is set |
Allow DELETE / Restrict DELETE |
Allow or restrict DELETE data events. |
neither is set |
ACLs Illustrated
A very simple example it illustrate this point:
-
There are three zones: Zone-X, Zone-Y and Zone-Z each with two adaptors. All adaptors are capable of storing/retrieving data entries for the Customer domain
-
Zone-X has the following Outbound ACL Chain
| Source Zone | Destination Zone | Destination Adaptor | Domain Version | Policy | |
|---|---|---|---|---|---|
1 |
Zone-X |
Zone-Y |
ALL |
ALL |
ALLOW ALL |
2 |
Zone-X |
ALL |
ALL |
ALL |
RESTRICT ALL |
ALL = GET, PUT, POST, DELETE
-
A Customer PUT data event is raised on adaptor1 in Zone-X
-
YOUnite can see that the adaptors in ZoneY and ZoneZ are all capable of consuming this data event
-
YOUnite inspects Zone-X’s outbound ACL chain and gets a match on the first ACL in the chain and routes the event to the two adaptors in Zone-Y
-
The first ACL does not match but the second does restricting the event, so the data event is NOT routed to Zone-Z
-
Following is more involved example using the zones and adaptors from above. ACLs are evaluated from first to last, the first match is applied to an incoming data event:
| Source Zone | Source Adaptor | Destination Zone | Destination Adaptor | Domain Version | Data Records | Policy | Notes | |
|---|---|---|---|---|---|---|---|---|
1 |
Zone-X |
ALL |
Zone-Y |
ALL |
ALL |
ALL |
RESTRICT ALL |
Restricts all outbound data events to Zone-Y |
2 |
Zone-X |
ALL |
Zone-Y |
Adaptor1 |
ALL |
ALL |
RESTRICT ALL |
This ACL is useless since ACL #1 already restrict all events to Zone-Y |
3 |
Zone-X |
ALL |
Zone-Z |
ALL |
Customer v1 |
DR-123, DR-456 |
RESTRICT ALL |
Restricts the data records (DR-123 and DR-456) from going to Zone-Z. |
4 |
Zone-X |
Adaptor2 |
ALL |
ALL |
ALL |
ALL |
RESTRICT ALL |
Restricts data events from flowing out of Zone-X’s adaptor2 to all zones. |
5 |
Zone-X |
ALL |
ALL |
ALL |
Customer v1 |
Customer.ssn |
RESTRICT ALL |
Restricts a customer’s SSN from flowing out of of Zone-X. |
6 |
Zone-X |
ALL |
ALL |
ALL |
ALL |
ALL |
ALLOW ALL |
Allow everything else out i.e. if a data event can be delivered to many adaptors in the YOUnite Data Fabric it will be delivered to all adaptors except for the restrictions placed by the above ACLs. ALLOW ALL is the default so in reality, this ACL is unnecessary. |
ALL = GET, PUT, POST, DELETE
After applying all of the above, the end result is:
-
Zone-Y gets nothing
-
Zone-Z is restricted from seeing the two DRs listed above
-
No data from Zone-X’s Adaptor2 flows to any zones or adaptors
-
Zone-X never shares the Customer version 1 Domain property Customer.ssn (for all adaptors in the outbound zones)
Complete ACL Data Flow Illustration
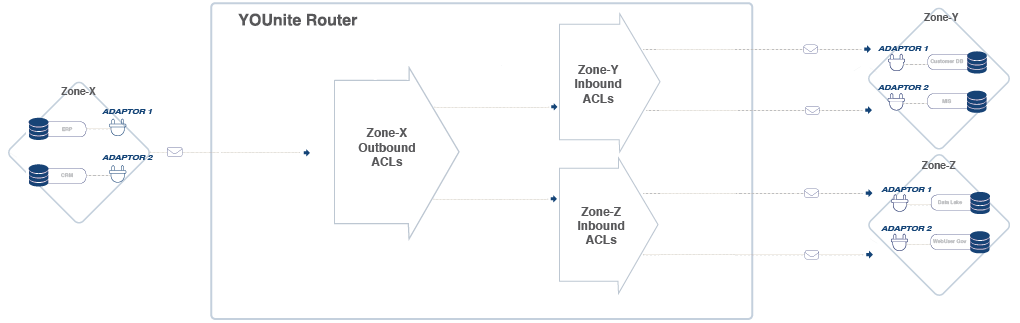
The image below represents the components involved as a data event is detected at an adaptor and flows through the YOUnite Data Fabric.
-
On the diagram’s left side a source zone’s single Source Adaptor (Zone-X, Adaptor 1) detects a data event in the source system (ERP) and sends a data event (data record for a given domain version) to the router.
-
Next, the data records from the source zone’s domains/adaptors are linked to YOUnite Data Records to avoid data record duplication.
-
Note: The data records published by the source adaptor could be updates, deletes, or new records.
-
-
Outbound ACLs then get applied to the source adaptor’s data record (Zone-X, Adaptor 1). The Outbound ACLs are defined by the source zone’s ZDS and define what data the Zone can send out (i.e .restricting data, or elements of data, of certain domains from flowing out of certain adaptors in the zone to other zones).
-
Destination zones have Inbound ACLs in place to define which data operations are allowed to flow in from source zones and their adaptor(s). Inbound ACL is defined by the destination zone’s ZDS.